What Is Ethical Hacking?
At its core, ethical hacking is the art—and science—of testing digital systems for weaknesses, but with a twist: it's done legally and with full authorization.
Think of it as breaking into your own house to make sure the locks work. These "white-hat" hackers simulate cyberattacks on everything from networks and firewalls to mobile apps, mimicking real-world threats in order to strengthen security.

⌨️ KEY CONCEPTS
Threats
Anything that could potentially damage a system - malware, phishing, DoS attacks.
Vulnerabilities
The flaws in a system that make damage possible - bugs, misconfigurations.
Exploits
Methods or code that leverage vulnerabilities, often delivering malicious payloads.
Attack Vectors
The routes hackers might take to breach a system - network, software, human.
Zero-Day Vulnerabilities
Flaws developers haven't yet discovered - the most dangerous threats.
Payloads
The malicious code or actions that occur after successful exploitation.
👨💻 THE HACKER SPECTRUM
WHITE HAT
The good guys, working legally to protect systems.
BLACK HAT
Malicious hackers breaching systems for personal gain.
GRAY HAT
Break rules without clear malicious intent.
SCRIPT KIDDIE
Use tools without understanding them.
HACKTIVIST
Hack to promote social or political causes.
🛠️ HACKER TOOLKIT
 Reconnaissance
Reconnaissance
- whois Domain registration lookup
- Shodan Search engine for devices
- nslookup DNS information gathering
Scanning
- Nmap Network mapping and port scanning
- Nikto Web server vulnerability scanner
- Dirb Directory brute-forcing
Exploitation
- Metasploit Penetration testing framework
- Burp Suite Web traffic interception
- SQLmap SQL injection testing
Post-Exploitation
- Mimikatz Credential extraction
- Cobalt Strike Post-exploitation framework
- Bloodhound AD enumeration and visualization
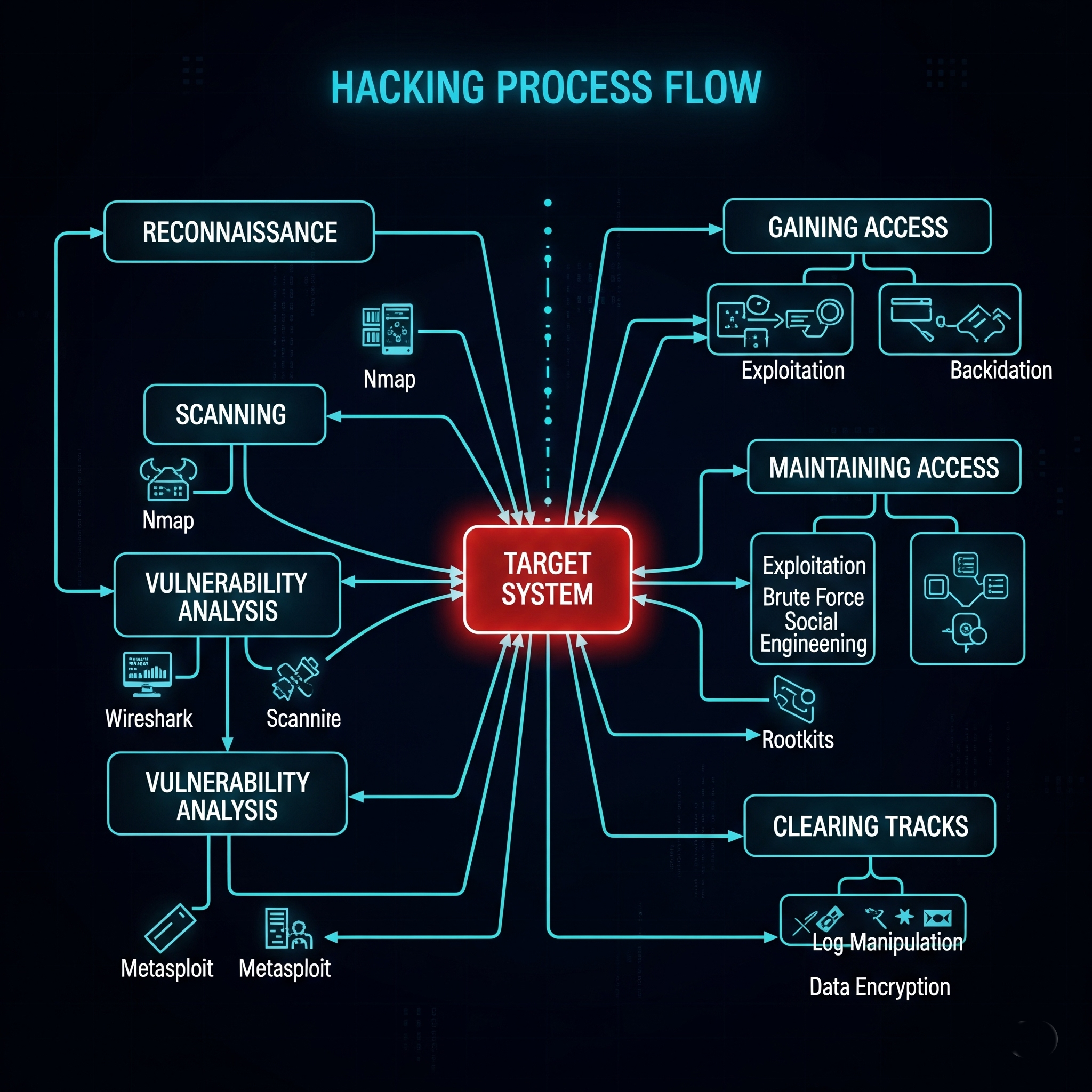
🔍 HACKING PROCESS PHASES
Reconnaissance
Passive/active information gathering
Scanning
Identifying live systems and weak spots
Gain Access
Exploiting found vulnerabilities
Maintain Access
Creating persistent footholds
Cover Tracks
Removing evidence of intrusion
🧪 TESTING TYPES
Black Box Testing
Tester has no knowledge of the target system (external attacker perspective)
White Box Testing
Full access to source code and documentation (internal knowledge)
Gray Box Testing
Limited insider knowledge (hybrid approach)
💼 CAREER PATH & CERTIFICATIONS
Recommended Certifications
- CEH Certified Ethical Hacker (Entry-level)
- eJPT Junior Penetration Tester (Practical)
- OSCP Offensive Security Certified Professional
- CRTP Certified Red Team Professional
- CPENT Certified Penetration Testing Engineer
Practice Resources
- HTB Hack The Box (Challenges & Labs)
- THM TryHackMe (Guided Learning)
- DVWA Damn Vulnerable Web App
- Juice Shop OWASP Vulnerable Web App
- Vulnhub Free Vulnerable VMs